16 Costly Airport Mistakes That Instantly Make You a Target in Your Arrivals or Departure Journey.

TL;DR: The vulnerabilities and how security experts recommend the following precise actions to help mitigate these mistakes.
| Vulnerability | Mitigation Strategy |
| Home Burglary via Tags | Use incognito black zip ties on black zippers to draw less attention. |
| Digital Data Theft | Use a VPN, turn off Bluetooth, and utilize a "USB data blocker". |
| Security Line Theft | Stagger with a partner; place electronics last on the belt so they are unattended for the shortest time. |
| Baggage Claim Theft | Do not stop at the restroom; go directly to the carousel. |
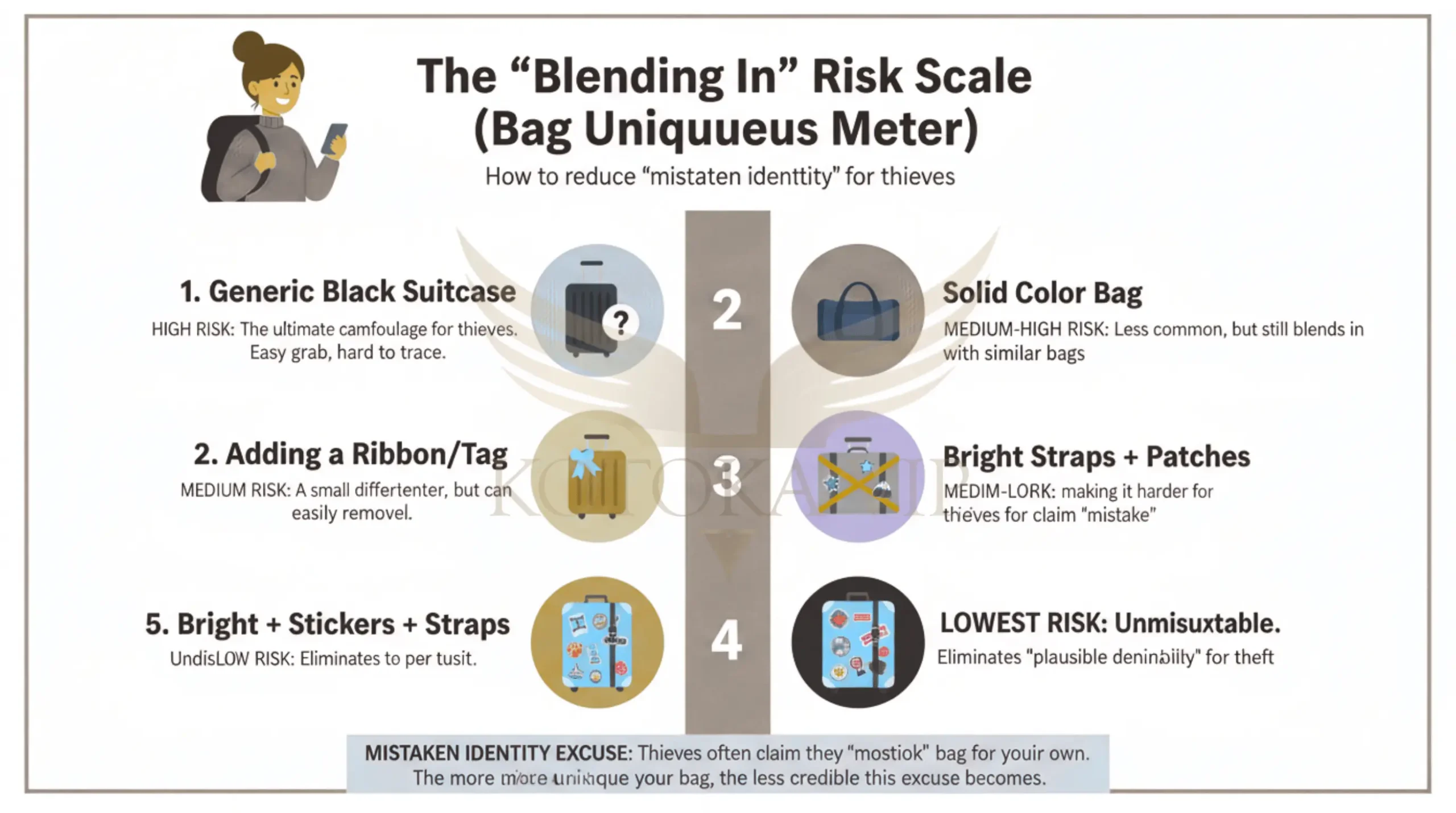
| Generic Bag Risk | Use stickers, bright straps, or unique patches to remove "plausible deniability" for thieves. |
| Post-Arrival Scams | Use only licensed taxis from designated stands and avoid airport currency kiosk. |
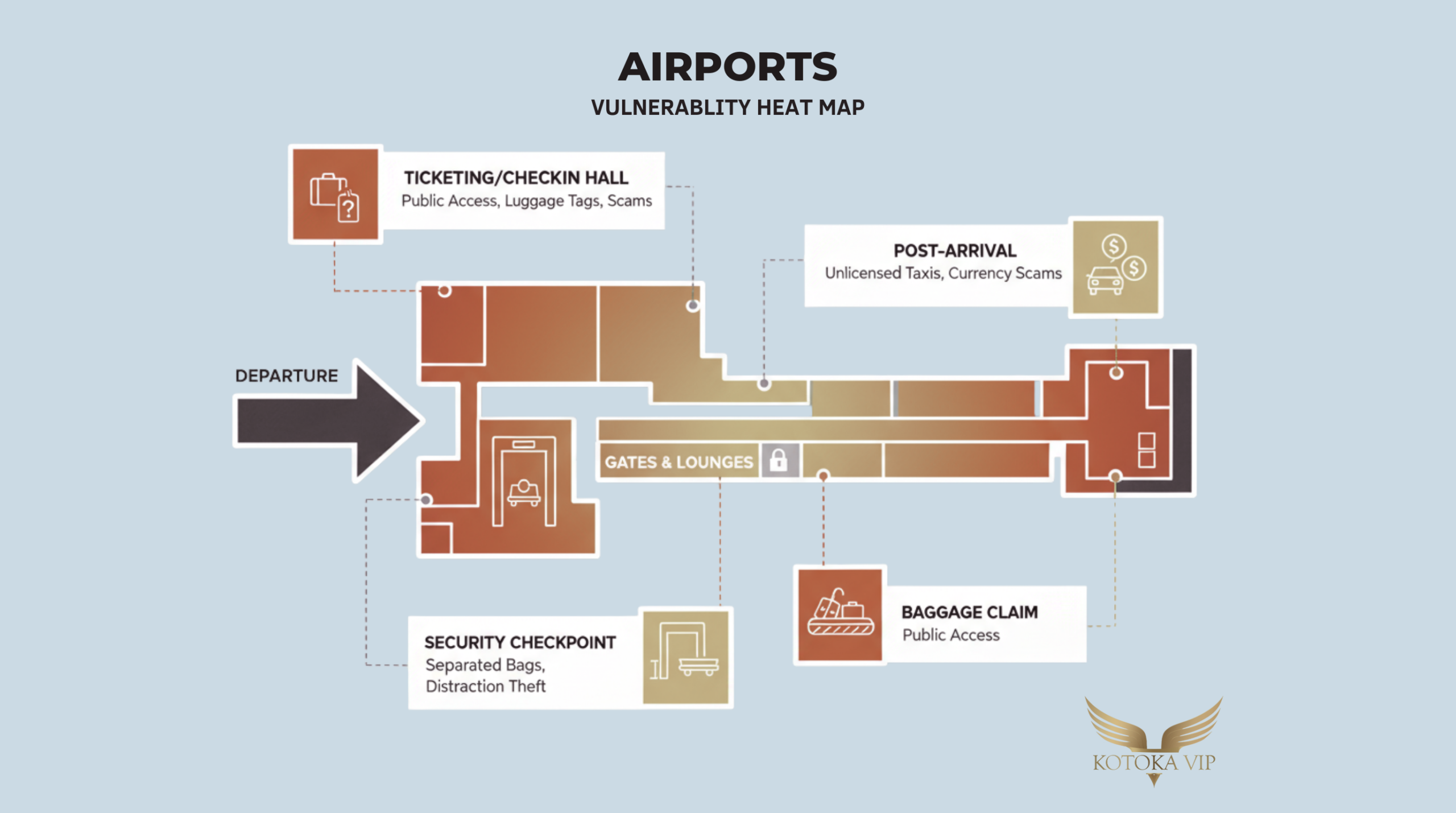
Airports are often perceived as some of the most secure environments in the world. However, security experts and crime data suggest a different reality. Travelers are frequently at their most vulnerable within the terminal.
In 2024 alone, Americans lost over $274 million to travel related scams, with the average victim losing nearly $1,000. These crimes often occur in "soft target" areas such as ticketing and baggage claim where public access is unrestricted.
The following analysis details the multifaceted vulnerabilities inherent in modern air travel, ranging from physical luggage theft to sophisticated digital exploitation.
Departure Vulnerabilities In The Pre-Security Phase.
The vulnerability begins the moment a traveler arrives at the airport. Professional thieves stalk departure areas specifically to identify high value targets based on their gear and behavior.

The Luggage Tag as a Burglary Map.
A primary physical vulnerability is the standard luggage tag. While intended for bag recovery, a tag displaying a home address serves as a confirmation of absence for criminals. One ex-professional thief, who admitted to over 20,000 home break-ins, specifically targeted airport check-in areas to gather addresses from luggage tags. This information tells a criminal three things. The house is empty, the owner is traveling and the owner likely has the disposable income to possess valuables.
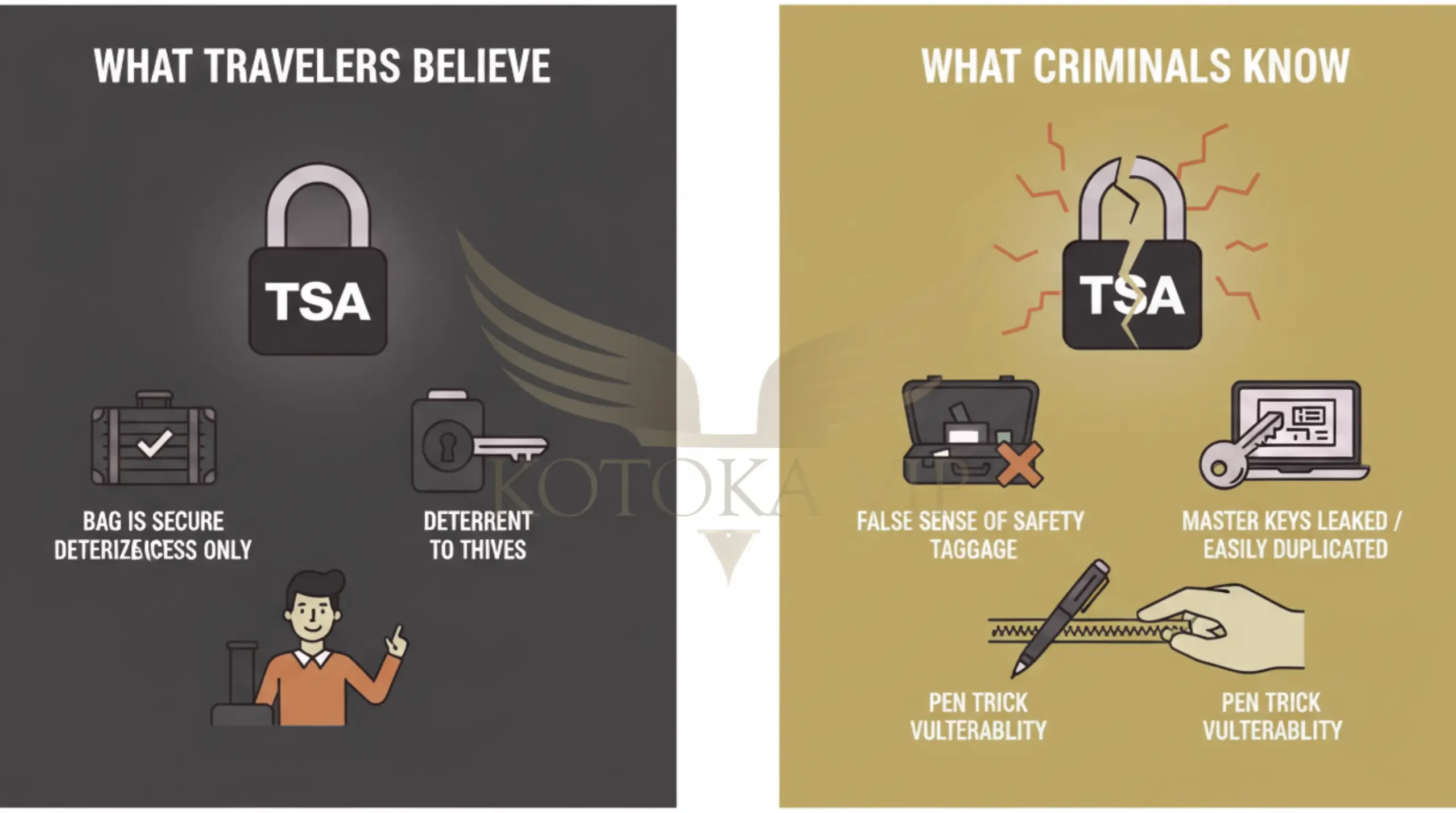
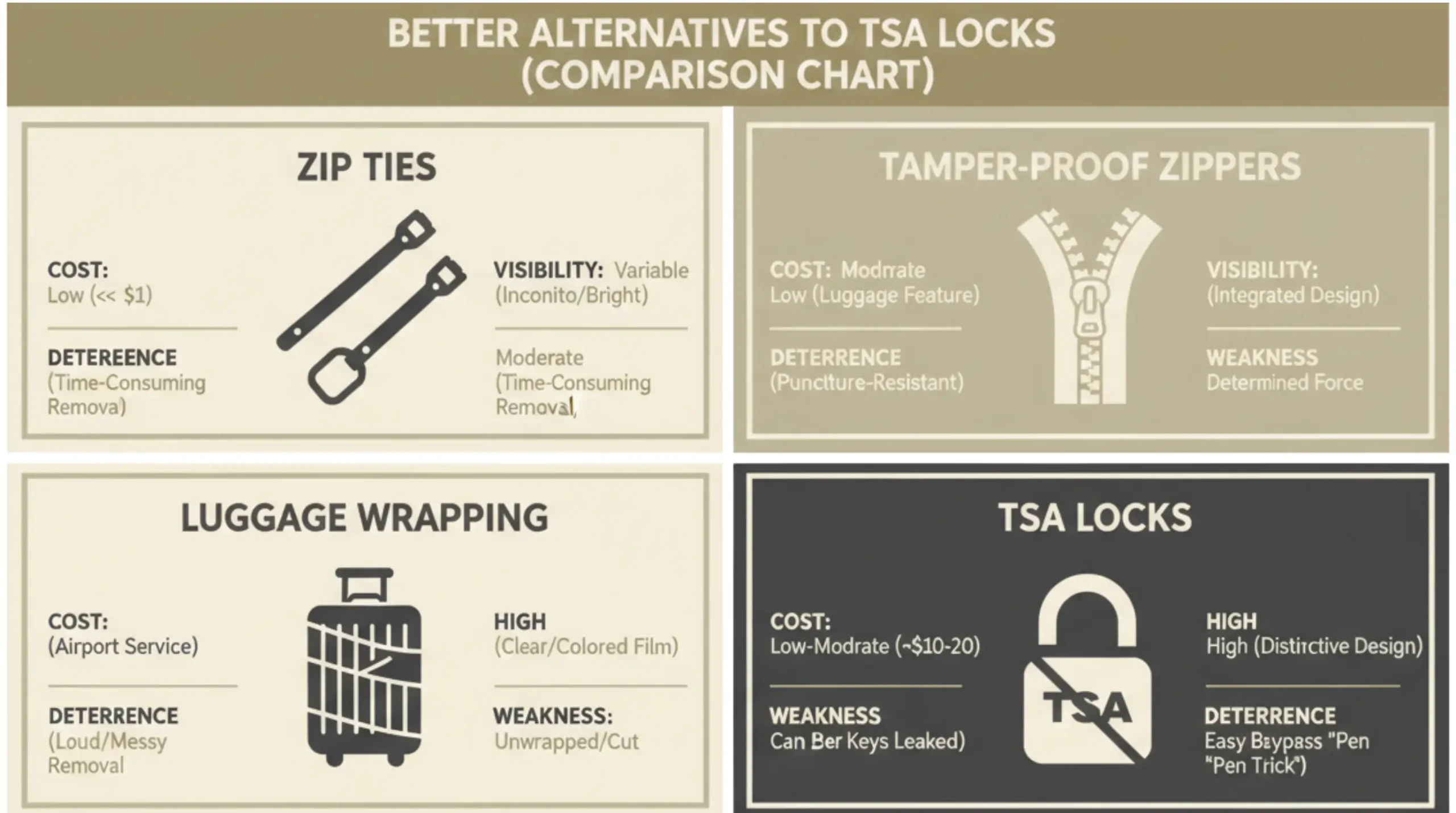
The Illusion of TSA Locks.
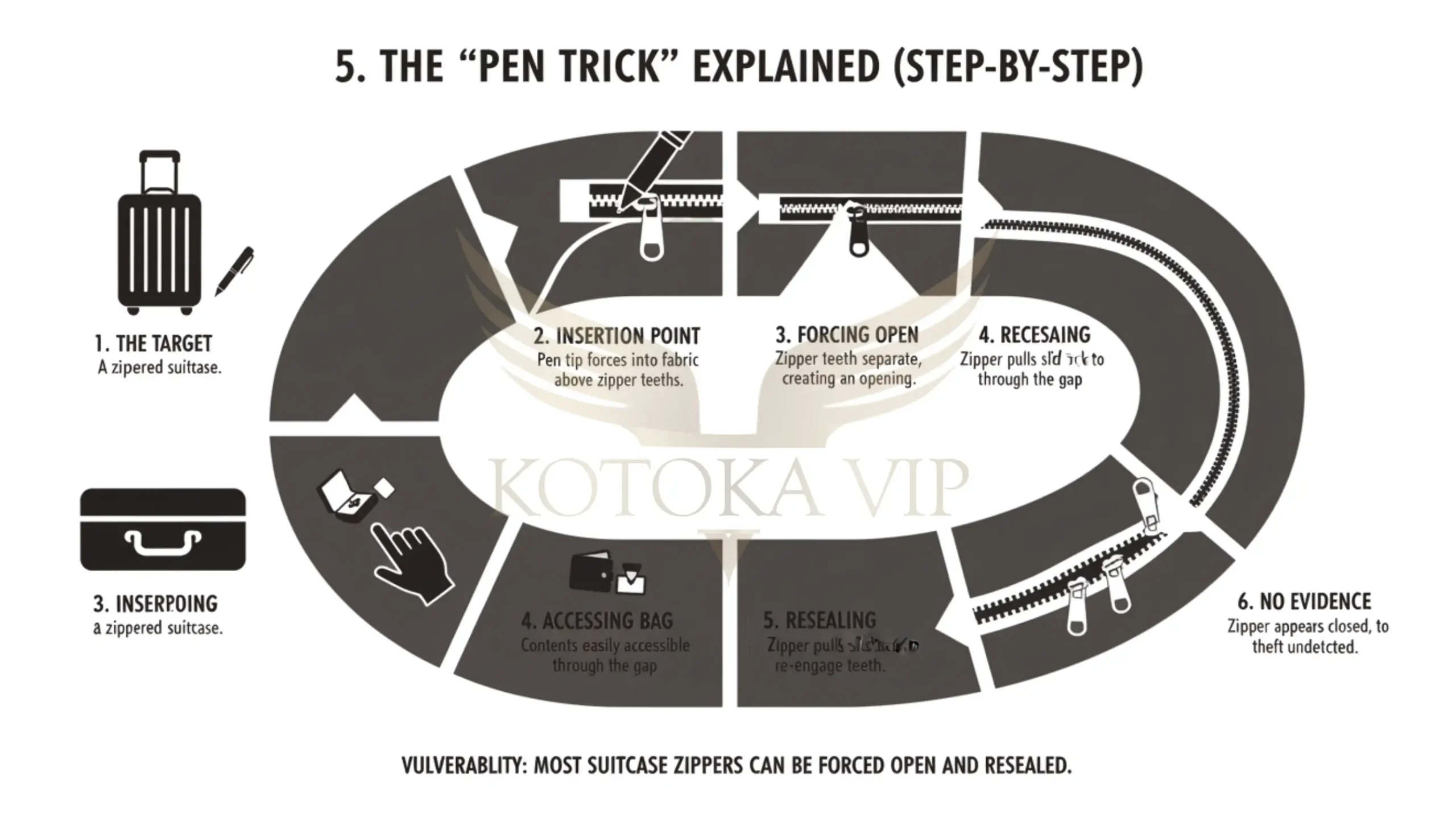
Many travelers rely on TSA approved locks, but these often increase vulnerability rather than decreasing it. Thieves assume travelers do not lock up worthless items; therefore a lock signals the presence of valuables, tipping the risk reward calculation in the thief's favor. Also the master keys for TSA locks have been leaked online, allowing criminals to 3D print or purchase them cheaply. Lastly most suitcase zippers are vulnerable to the pen trick, where a ballpoint pen is used to force open the zipper track. The thief can rummage through the bag and then slide the zipper pulls back over the gap to reseal it, leaving no sign of entry.
Check-In and Support Scams.
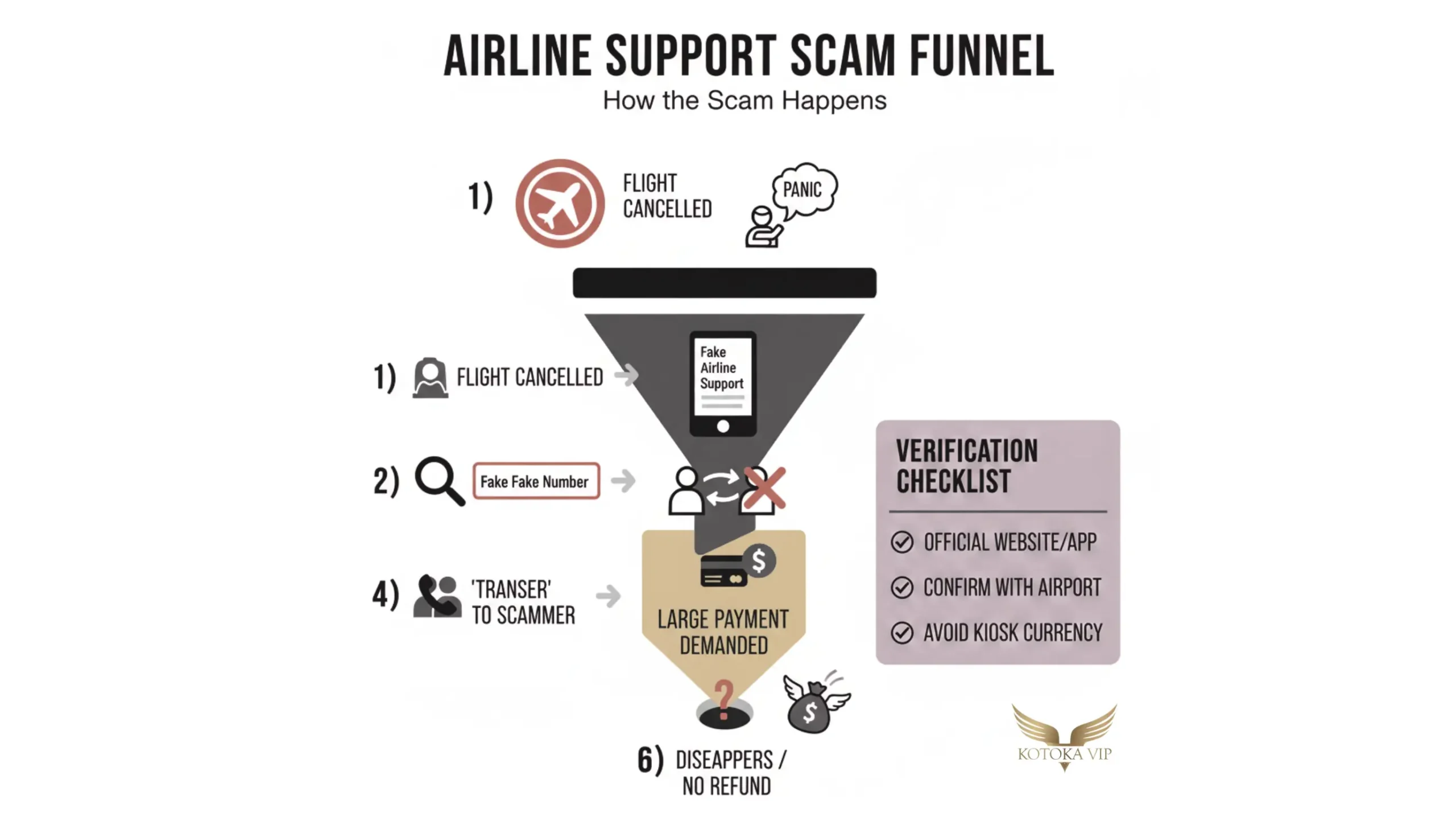
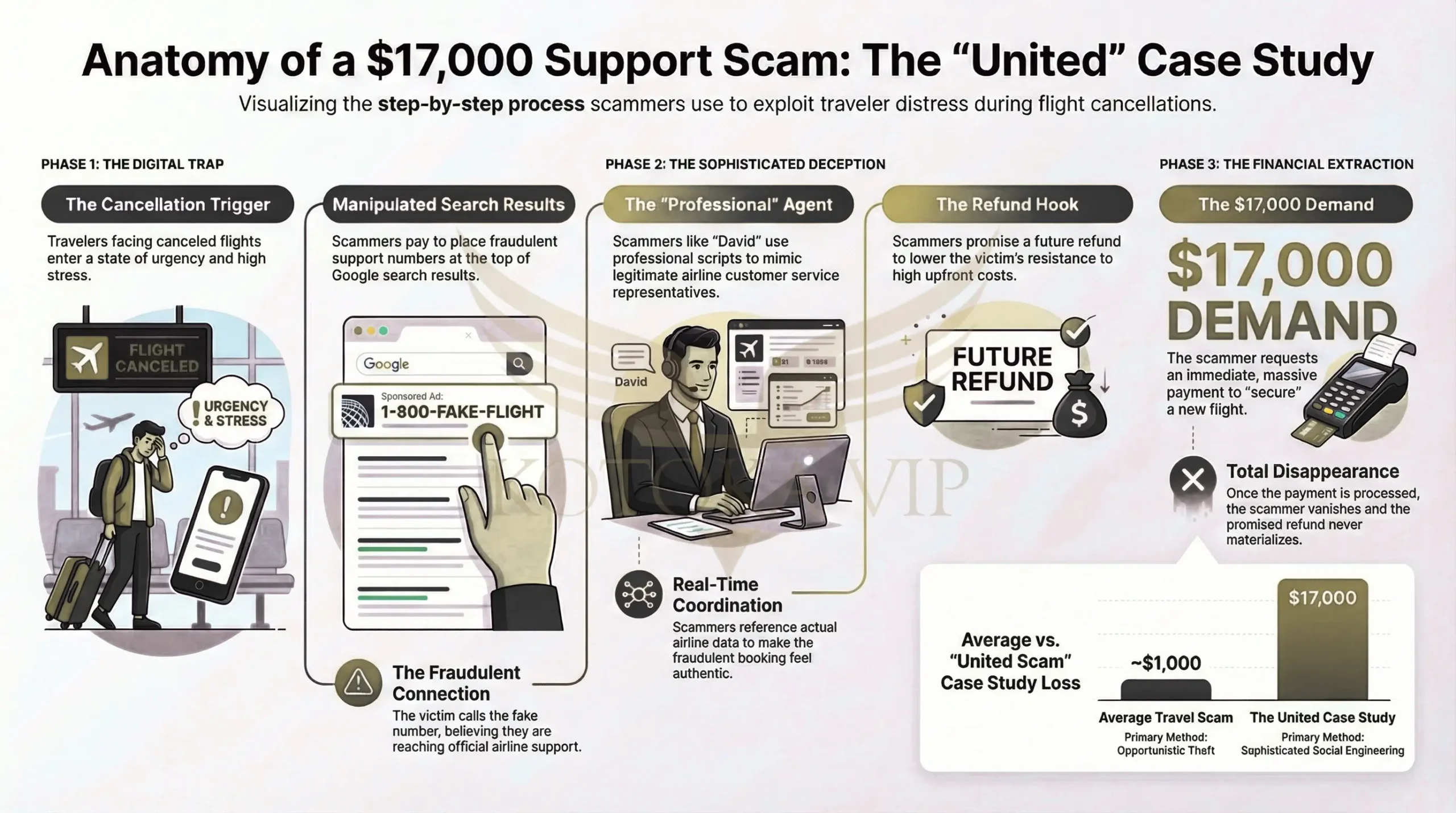
Stressed travelers facing flight cancellations are particularly susceptible to fraudulent customer service calls. Scammers manipulate search results so that fake airline support numbers appear at the top of Google .
Case Study: The $17,000 United Scam.
A traveler named Dan, whose United Airlines flight was cancelled, called a number he found online. The agent, appearing professional, transferred him to a scammer named "David" who claimed he could rebook the flight for an immediate payment of $17,000, promising a later refund. Because the scammer coordinated with the real airline to make the booking feel legitimate, Dan paid the fee, only for the scammer to disappear and the refund never to materialize.
Digital and Cyber Vulnerabilities.
Airports are high density environments for digital pickpocketing. Because travelers are desperate for connectivity and power, they often overlook basic security protocols.
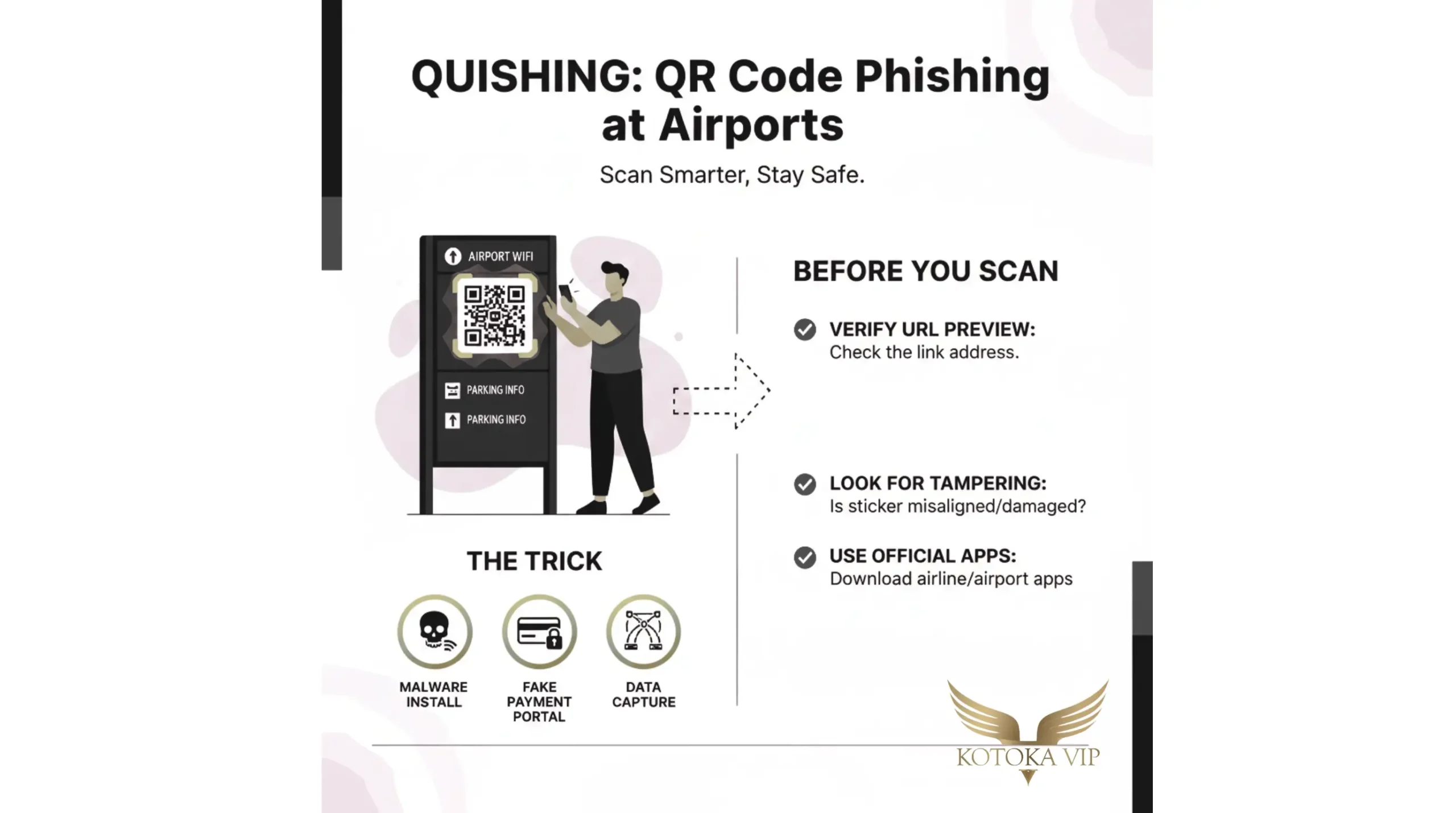
QR Code Phishing. ("Quishing")
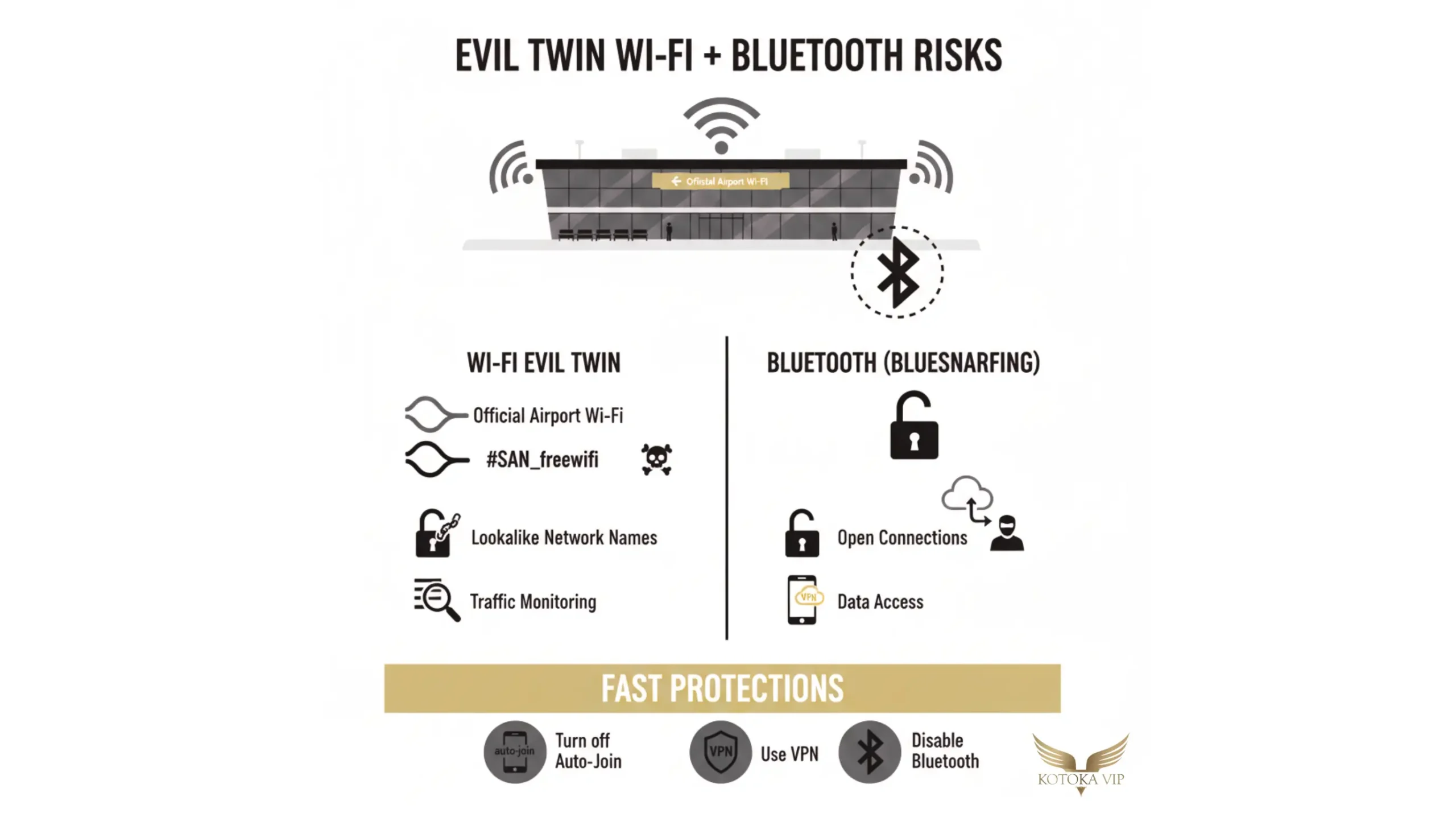
Wi-Fi and Bluetooth Exploitation.
Ghost Tapping and NFC Fraud.
In crowded areas like shuttles or boarding gates, scammers use hidden NFC readers to trigger tap-to-pay transactions from a victim's pocket. This ghost tapping can wake a phone and prepare a payment screen, leading a traveler to inadvertently approve a charge when they next unlock their device.
Juice Jacking. (USB Malware)
Public USB charging ports can be tampered with to install malware on devices. This juice jacking allows criminals to pull photos, messages, and passwords while the phone appears to be charging normally. The TSA has issued official warnings for travelers to avoid these ports in favor of standard wall outlets.
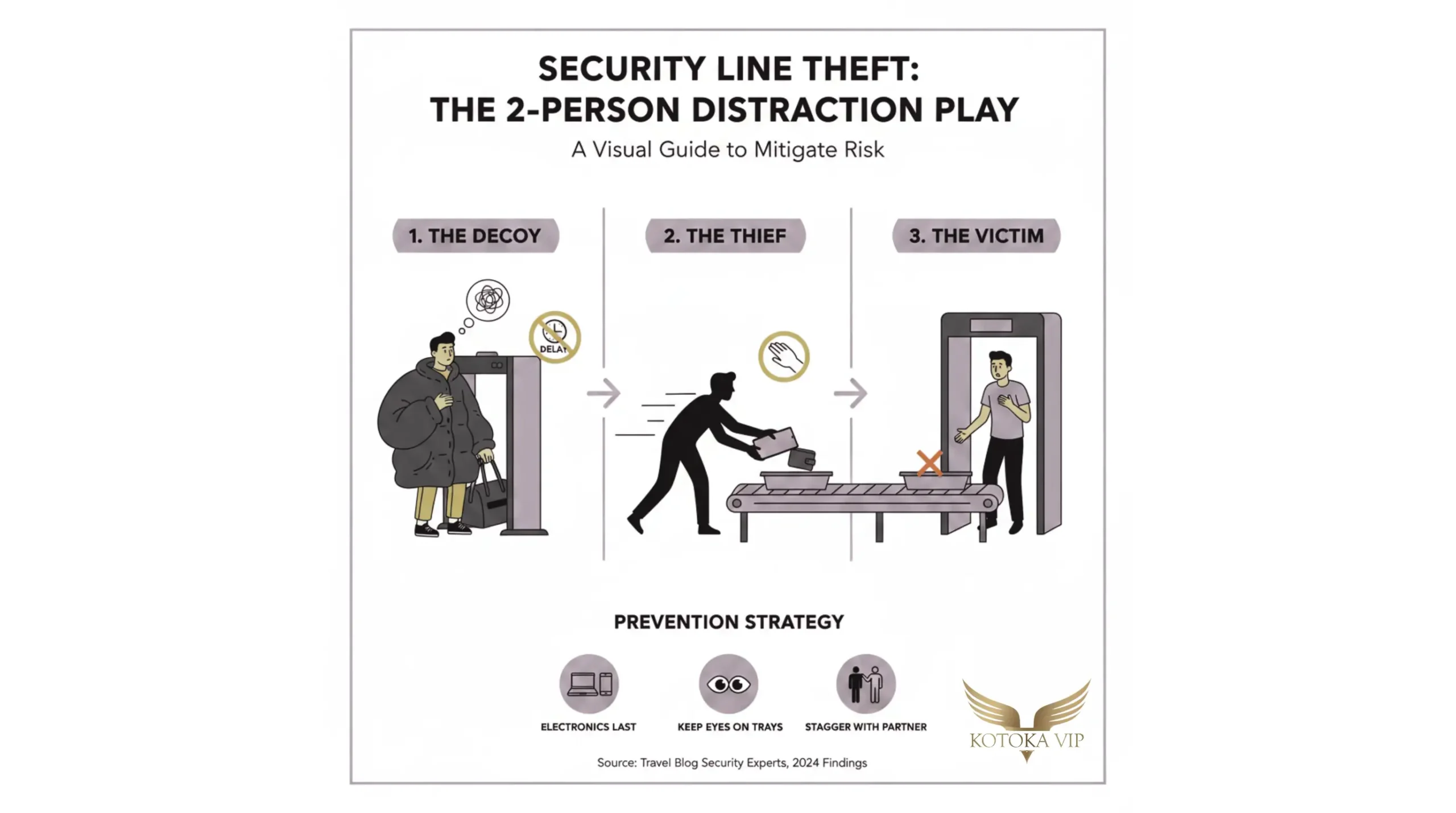
Security Checkpoint As Focused Vulnerability.
The security line is one of the few places where a traveler's belongings are intentionally separated from them, creating a window for distraction scams. These scams typically involve a two-person team. One person creates a delay at the body scanner (The Decoy), fumbling with bags or asking confusing questions to stall the line while their partner (The Thief), who has already passed through the scanner, grabs high value items (watches, wallets, tablets) from the victim's tray as they emerge from the belt.
Because dozens of passengers pass through every minute, it is nearly impossible to identify the thief once they have blended back into the terminal crowd.
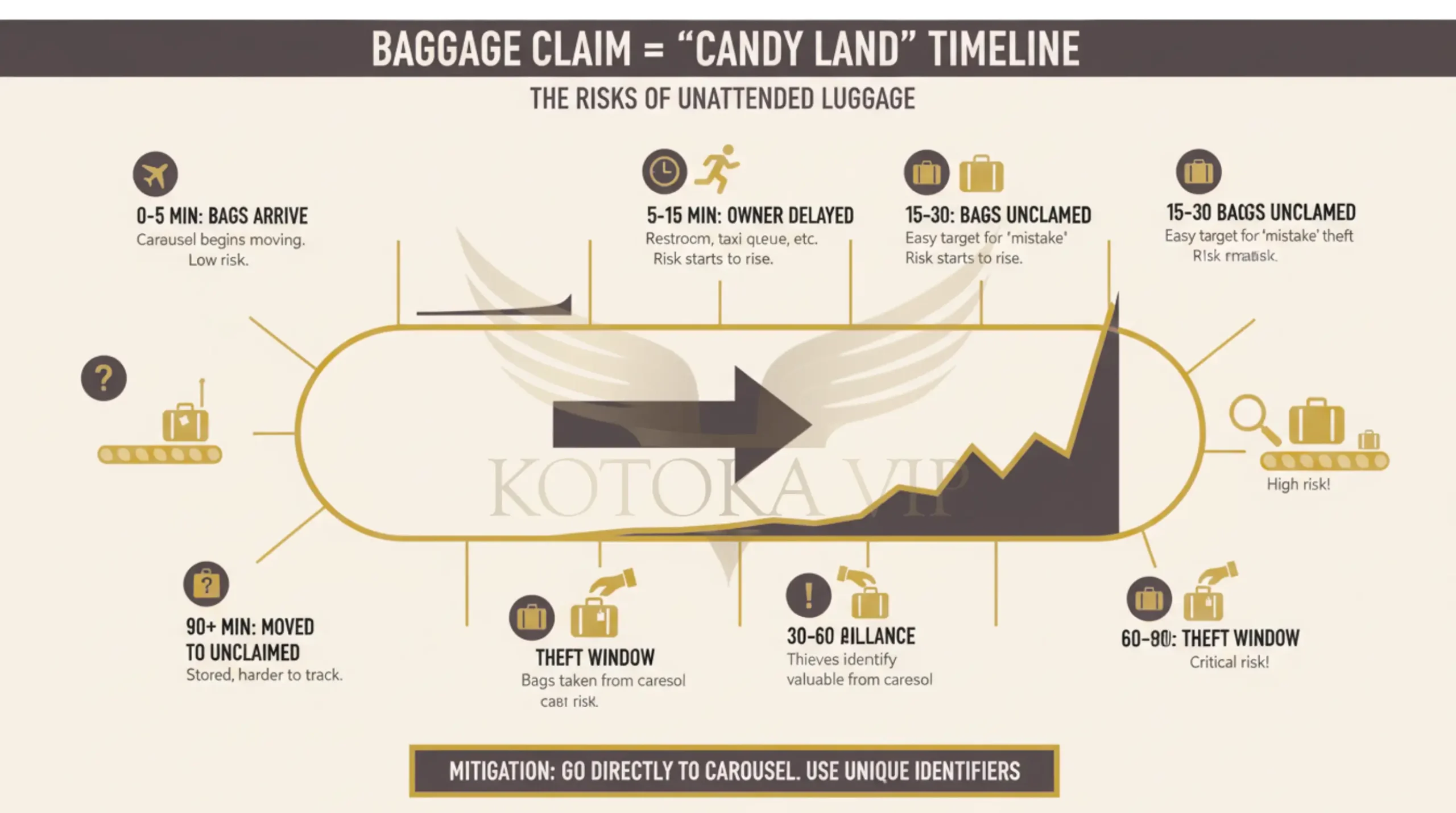
Arrival Vulnerabilities Using The Baggage Claim As Candy Land.
The baggage claim area is perhaps the most insecure part of the airport because it is often open to the public without ID or boarding pass checks.
Opportunistic Theft at the Carousel.
Thieves frequently reach the baggage claim before the passengers. If a traveler stops at the restroom or for coffee, their bag may rotate on the carousel unattended, making it an easy target. Statistics show that airports with long walks from gates to carousels have higher theft rates.
Ranks #1 globally for baggage theft, partly due to the 20 minute walk to the reclaim area is the London Heathrow (LHR). The Dallas-Fort Worth (DFW) features a 43 minute walk, giving thieves ample time to intercept bags. Lastly the Paris Charles de Gaulle (CDG) experiences high theft rates linked to its 25 minute gate to carousel gap.
Unclaimed Luggage Areas.
When bags are not picked up, airlines move them to cordoned-off unclaimed areas. Thieves view these as candy land because it confirms the owner is not present. Surveillance footage has captured individuals brazenly walking into these areas, distracting lone employees, and walking off with multiple suitcases.
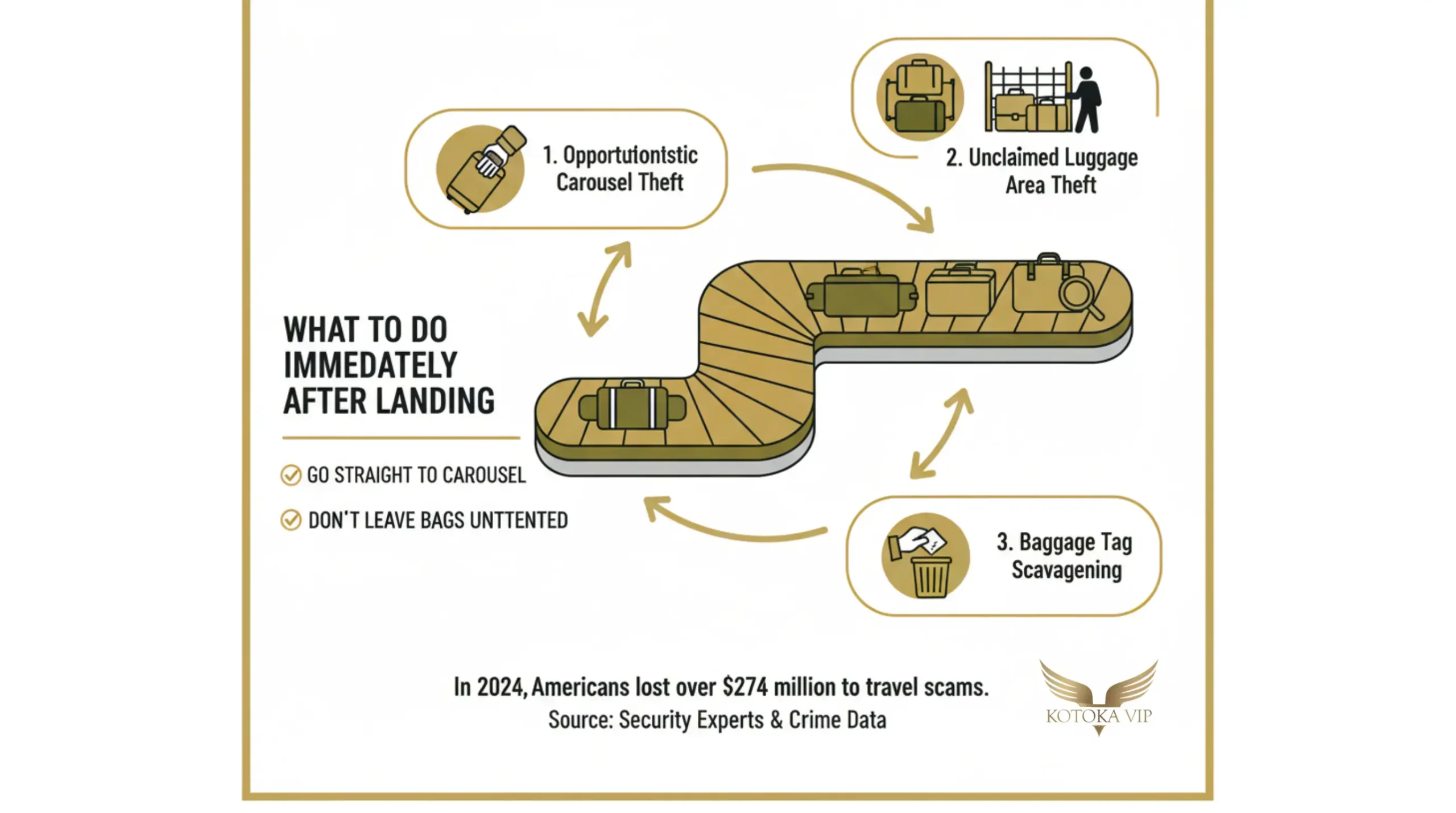
Baggage Tag Scavenging.
The Plausible Deniability Principle.
Professional thieves often target generic black suitcases. If caught, they use the excuse, Oops, wrong bag, my bad, to avoid prosecution. A thief is significantly less likely to target a unique, neon-colored, or heavily decorated bag because it removes this excuse and makes them more visible to security.
Post-Arrival Transportation and Currency Scams.
Upon exiting the secure terminal, travelers face a final gauntlet of scams designed to exploit their lack of local knowledge.
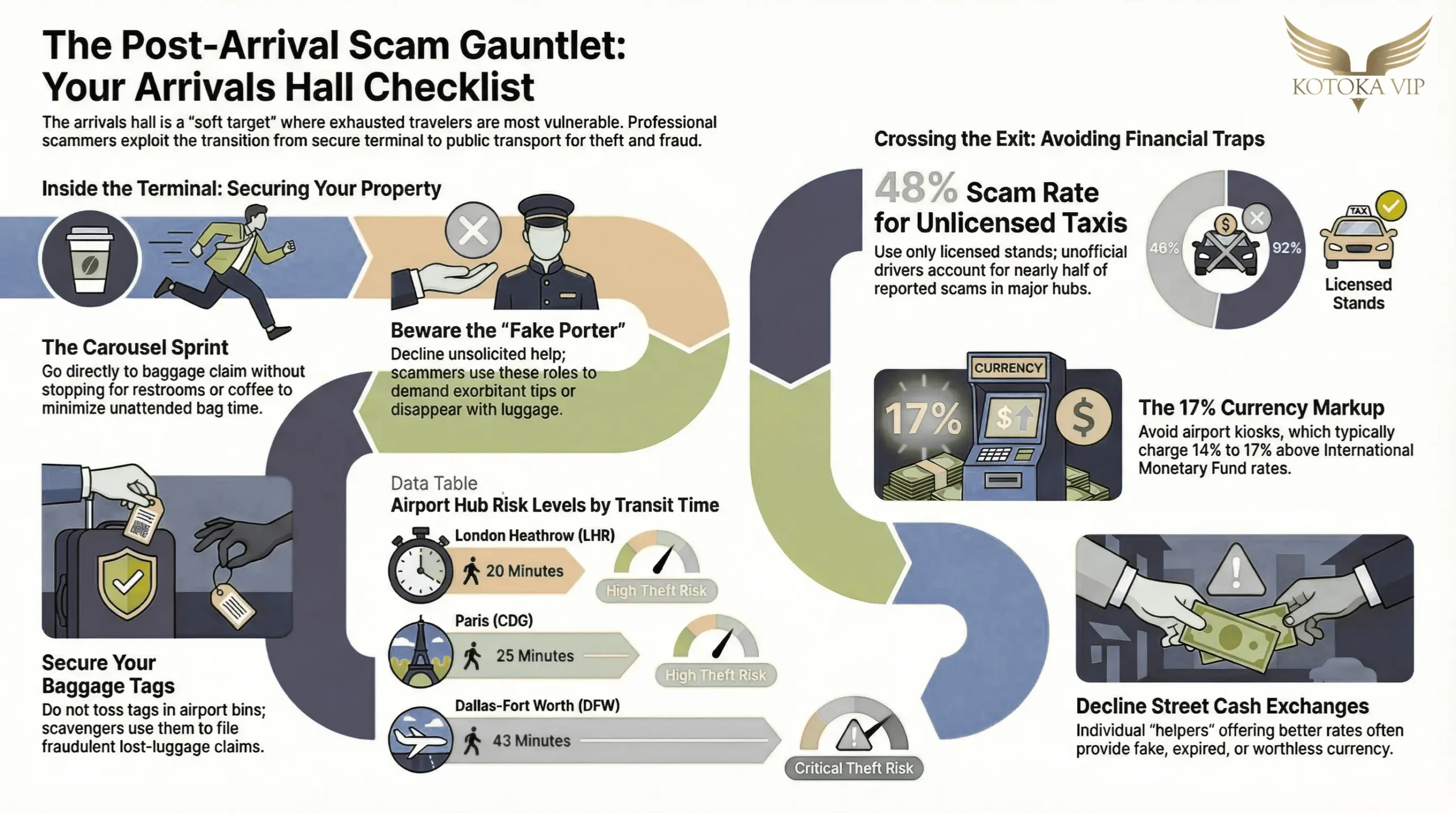
Unlicensed Taxis and Ride-Shares.
Unlicensed drivers often wait in arrival halls, posing as legitimate ride-share drivers or airport staff. These individuals frequently overcharge, take unnecessarily long routes, or use Bluetooth skimmers to capture payment card data during the transaction. In cities like Bangkok and London, overcharging by unofficial drivers accounts for 34% to 48% of reported travel scams.
Currency Exchange Rip-Offs.
Airport exchange kiosks often charge 14% to 17% above the International Monetary Fund reference rate. More dangerously, individuals may approach travelers offering better rates in cash. In European hubs like Prague, these scammers often provide expired, fake, or different-currency bills that are worthless to the traveler.
Fake Porters and Helpers.
In many international airports, individuals posing as official porters will insist on helping with luggage, only to demand exorbitant tips or disappear with the bags entirely.
Insider Threats and Systematic Failures.
While most theft is opportunistic, some vulnerabilities are systemic and involve airport staff. 14 baggage handlers were arrested for stealing nearly 2 million euros worth of items from checked luggage. They would open bags in the plane's hold, steal valuables, and reseal them before they reached the carousel at Tenerife South Airport in 2023. Sometimes rogue employees may falsely claim a bag is overweight and demand cash only payments at a private desk a trick known as overweight baggage trick.
To summarize.
Airports remain a high risk environment because they are transitional spaces where travelers' physical and digital guards are lowered. By recognizing that thieves look like us and blend into the crowd, travelers can adopt the habits necessary to protect their identities, their property, and their homes.